Maybe I’m crazy, but I’ve just joined my 12th startup at the age of 63. Kosli is the product I’ve been looking for since I started talking about this idea five years ago, but until recently I couldn’t find anyone who wanted to build it. That all changed when I ran into the Kosli founders at DevOpsDays DC back in September 2022.
As I join Kosli, I’m reminded of when I joined Chef in 2010 just as the infrastructure of the code era was starting. If my instincts are correct, Kosli will be a similarly fantastic ride for the next ten years in DevOps and modern governance. But how did I wind up on a road that led to joining a Norway based startup at DevOpsDaysDC?
Researching DevOps and Audit
In 2014 Gene Kim, an author of the Phoenix Project, invited several DevOps industry leaders out to Portland to work on what we now call the Guidance Papers. The following year DevOps and Audit was discussed and we produced a paper called An Unlikely Union: DevOps and Audit. The purpose of this paper was to discuss how new software delivery patterns like DevOps can help us to rethink IT security risk policy, particularly “Separation of Duties.”
Topo Pal of Capital One wrote a blog post, Focusing on the DevOps Pipeline, in 2018. In that post there was a section called Creating Better Pipelines. It described how pipelines could be designed, measured, and improved using “gates.” It outlined 16 principles:
- Source code version control
- Optimum branching strategy
- Static analysis
- >80% code coverage
- Vulnerability scan
- Open source scan
- Artifact version control
- Auto-provisioning
- Immutable servers
- Integration testing
- Performance testing
- Build deploy testing automated for every commit
- Automated rollback
- Automated change order
- Zero downtime release
- Feature toggle
Teams could bypass the Change Advisory Board (CAB) using this mechanism. A team could get an exception from submitting a change to the weekly CAB if they enabled the 16 attestations (evidence) in their software delivery.
The same year, we started working on another paper called Dear Auditor at Gene’s IT Revolution forum. Initially, the paper apologized to the auditors as follows:
With all this growth, we made a mistake, we forgot to bring you along for the ride. That is totally our bad, but we want to make it right. We want to make some new commitments.
- We will bring you along
- We will be fully transparent about our development process
- We do realize that we own the risks
- We will maintain an open channel of discussion to demonstrate to you how we manage risks with our modern development practices
There is only one apology page, and the rest of the paper contains a Risk Control Matrix (RCM). Among the ten categories of the RCM, 53 risks were identified.
- Unauthorized changes to production (PAM)
- Prod breaks due to human error (IAC)
- Material misstatement of financial data (SOD)
- Intellectual property and licensing violation (SBOM)
- A data breach from unauthorized access (DAR)
- Unwanted customer impact (Deployment Strategies)
- Business continuity (BCM/DR)
- Divergence of audit evidence from developer evidence (DAG)
- Data in appropriate jurisdiction (GDPR or PII)
- Compromise unknown breach of infrastructure (Red Team)
Topo and I started talking about the real-world issues associated with number 8 on the RCM - divergence of audit evidence from developer evidence, which we’d later call DevOps Automated Governance (DAG). The biggest issue with this category was the low efficacy and high toil of IT Internal Audit.
DevOps Automated Governance
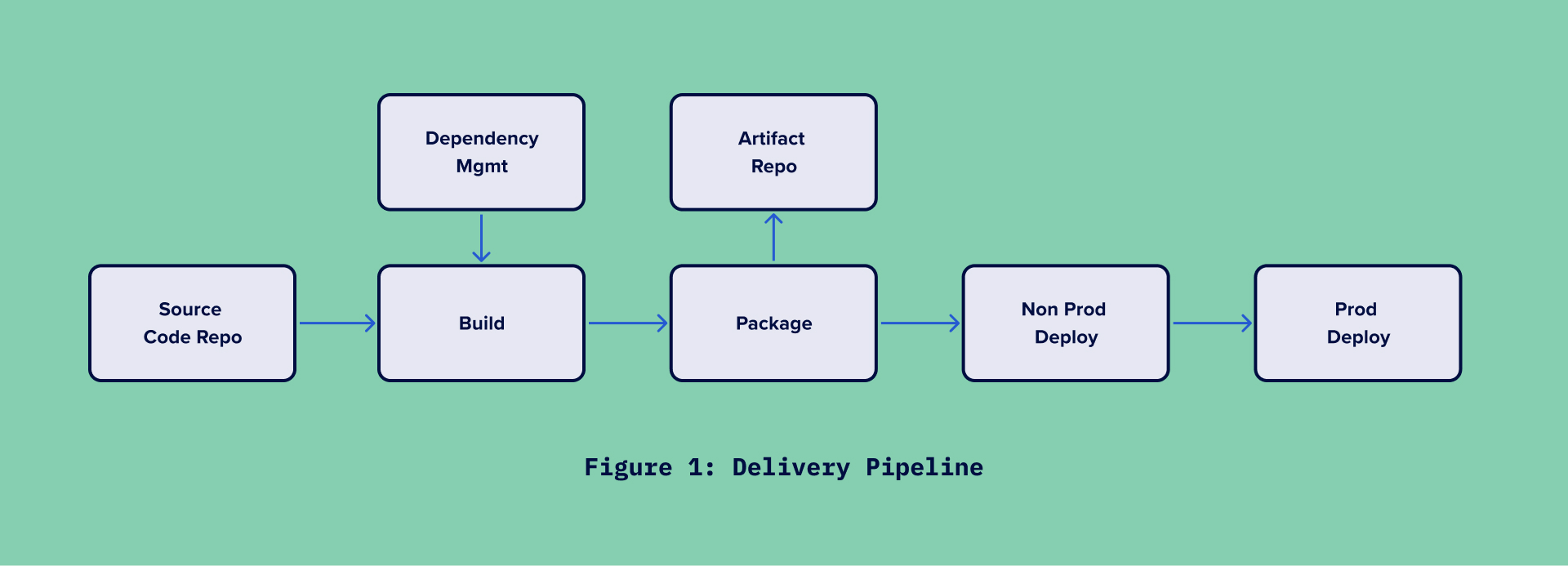
We decided that there might be a way to do something different with IT Risk and Internal Audit based on his 2018 blog article and the Dear Auditor letter. We wrote a paper titled DevOps Automated Governance Reference Architecture in 2019. To achieve this, we developed a software service model that includes attestations (signatures) built into the delivery pipeline that correspond to risk control measures. We described the delivery pipeline in seven stages.
We identified 37 specific risks and 37 opportunity attestations (evidence) among the seven stages. The initial idea was to use something like blockchain because our intention was that the attestations should be digital and immutable i.e. non-tamperable. Grafeas was a tool used by Google to audit and govern its software container supply chain and was recently released as an open source project. We chose Grafeas for the reference implementation over a blockchain solution.
A top five bank in the US implemented the reference architecture after the paper was released. As part of the project, I was able to provide advice. By 2021, we decided to develop an updated guide based on the original 2019 paper and the work done by this bank and a few other organizations. We created a novella instead of another bland reference architecture.
Writing Investments Unlimited
Using a chronic core conflict and a hero’s journey, we wanted to tell a story in the style of The Phoenix Project. We imagined a company called Investments Unlimited and the story begins as it is about to receive a Matter Requiring Immediate Attention (MRIA) from the Office of the Comptroller of the Currency (OCC).
In The Phoenix Project, Eric Reid guides Bill Palmer through the journey of Parts Unlimited Corporation. In Investments Unlimited, Jason Colbert guides Bill Lucus through his journey. After reading the novella, IT Revolution Press asked us if we wanted to turn it into a full-length novel. We released it as Investment Unlimited on multiple best-seller lists a year later, in September 2022.
The book’s release coincided with the end of my three-year contract with Red Hat. As a result of the book’s success, I considered starting another business on my own. However, at 63, my wife and I decided it might be too much. Then, at the DevOpsDaysDC conference in September, I ran into the founders of Kosli.
Meeting Kosli at DevOpsDaysDC
Mike Long, the co-founder of Kosli, demonstrated how his product does all the things mentioned in Investments Unlimited during an open spaces session. They had implemented a system I had wanted to build since 2017. Customers used their system for DevOps Graph data as well as Automated Governance. Mike and James Logan, the other founder, discussed how I might best fit into their company over the next month. They nailed it when they said they wanted me to join as a Distinguished Researcher.
I noticed this opportunity was uncannily similar to what happened to me in 2009. Infrastructure as Code (IAC) was something I believed in very early on. And, as with Mike and James, I met Adam Jacob and Jessie Robbins at a conference - O’Reilly Velocity. Adam and Jessie then asked me to join their startup, Chef (formerly Opscode).
Back then, Chef had just raised a seed fund of $2 million and had nine employees. Recently, Kosli raised $3 million with 12 employees. Mike reminds me a lot of how Adam was and James a lot like Jessie (which is a tremendous compliment to Mike and James). In addition, just as I predicted in 2009 that IaC would play a significant role in IT over the next ten years, DAG will play an important role in the coming decade.
Coming full circle with Heavybit
But the icing on the cake came when I discovered that Kosli’s lead investor was Joe Ruscio, the founder of Librato, an early DevOps monitoring company. Nothing warms your heart more than hearing that your lead investor says he remembers your 2010 DevOps State of the Union presentation from Silicon Valley DevOps Days.
Our VC firm, Heavybit, also includes Jessie Robbins as one of its investors. Heavybit represents a new breed of investors founded by software startup entrepreneurs. It’s a perfect match for us.
At 63, I feel like I’m 30 years old and ready to take on the world just as I did in 2010 when I joined Chef. Stay tuned to this space.
















