Kosli Changelog October 2024
Welcome to October’s edition of the Kosli Changelog. The season might be spooky, but the product updates we delivered this month are far from it. Quality over quantity is the motto for this month, …
Migration Announcement: Transitioning from Legacy Flows to Flows with Trails
We are excited to announce that we will be migrating your Kosli Flows data to Flows with Trails. This transition will unlock access to our latest features, such as the first-class Sonar integration, …
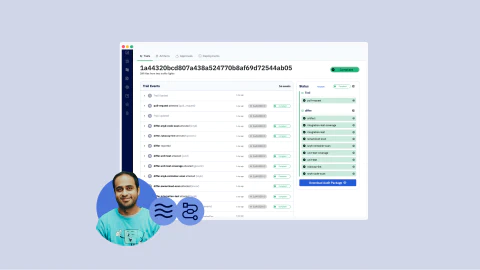
Using Kosli attest in Github Actions Workflows - Some Do's and Don'ts
The heart of Kosli’s functionality lies in its attest command. Think of it as a digital notary for your CI process. Every time you complete a significant step in your pipeline (e.g., a security …
Record an immutable record of all changes made to your LaunchDarkly feature flags with Kosli
We’re thrilled to introduce our latest integration with LaunchDarkly! This powerful combination allows you to keep an immutable record of all changes made to your feature flags using Kosli …
Kosli Changelog September 2024
Welcome to September’s edition of the Kosli Changelog. As we brace ourselves for a wet and wild autumn our focus remains sharp on delivering updates that enhance the compliance of your software …
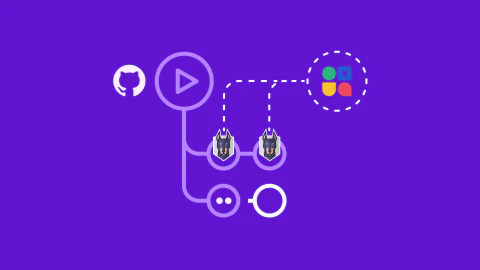
Introducing Kosli's Logical Environments: Gain total visibility and control over complex systems
In today’s fast-paced development landscape, environments are no longer simple or isolated. You’re managing resources that span across development stages, geographies, and technologies. And as those …
Streamline code quality: Integrating SonarCloud and SonarQube scanning with Kosli for automated compliance
Static code analysis is an important part of testing your software to ensure it is release-ready. In contrast to dynamic testing, which involves executing your code to find errors, static analysis …
Kosli Changelog August 2024
This month we are happy to announce that the logical environments feature is now live! This has been a big project for the team and we’re delighted to deliver it this month. Logical environments will …
Just the facts" 🔏 🗒️ Introducing Software Delivery Evidence Management (SDEM)
The DevOps Detective: “Just the facts” Picture a gruff-voiced sergeant from the classic TV series “Dragnet,” but instead of solving crimes, they are navigating the complex …
From lean manufacturing to DevOps: The software factory revolution
In our journey through the evolution of compliance in the DevOps era, we’ve seen the limitations of traditional compliance methods and the high stakes of compliance failures. Manual processes, …