Tags
How to achieve SOC 2 Type 2 in 90 days with Drata and Kosli
Every software purchasing decision has a security impact, and with information security threats on the rise, companies are increasingly concerned about third party vendor risks. That’s why for …
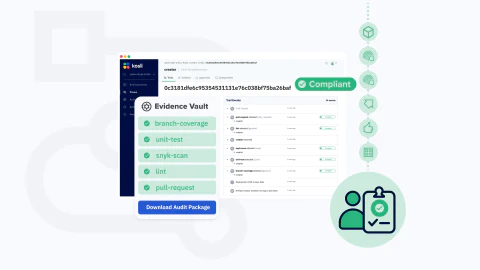
How to record an audit trail for any DevOps process with Kosli Trails
In this article I’m going to introduce Kosli Trails. This is a new feature that allows you to record an audit trail for any DevOps process. It’s already in production and being used to record …
How to track Infrastructure as Code changes in Terraform with Kosli
Infrastructure as Code (IaC) has emerged as a cornerstone for efficiently managing and provisioning infrastructure. Among the many tools available, Terraform has gained unparalleled popularity, …
Kosli Changelog - February 2024
It’s already March, the sun is starting to show up again here in Northern Europe, the snow is melting away, and the Kosli team has been hard at work, making good use of that extra leap day in …
Kosli Achieves SOC 2 Type 2 Compliance: Strengthening Our Commitment to Security
We are thrilled to announce that Kosli has successfully completed a SOC 2 Type 2 audit, demonstrating our commitment to the security, quality, and operational excellence our customers expect. This …
Kosli Changelog - January 2024
The Kosli team starts the new year with endless energy and some exciting news for you! This month, we’ve delivered not only bug fixes and performance improvements but also a couple of highly …
Maintaining Security with DevOps Compliance
DevOps teams play an increasingly important role in all types of software companies. From legacy organizations to cloud-native startups, the DORA metrics tell us that the performance of the DevOps …
How to build DevOps automations with Kosli Actions
Kosli allows regulated organizations to scale their continuous delivery so that they can deploy changes to production at maximum speed without the risk of non-compliance. It does this by recording all …
DevOps Change Management Resources
The DevOps Change Management Content Hub is a set of resources for modern software teams who struggle to align their DevOps automation with their change management requirements. In our experience, …
Continuous Compliance Content Hub
The Continuous Compliance content hub is a set of guides for DevOps teams who need to move fast while remaining in compliance for audit and security purposes. We know that the old change management …
Ready to Automate Governance?